NB: There's a known issue with the latest ISO release involving the network. Please add your DNS and gateway entries manually to the server. You can edit and use the following code:
echo DNS1=<ip of dns server> >> /etc/sysconfig/network-scripts/ifcfg-enp0s3
echo DNS2=<ip of dns server 2> >> /etc/sysconfig/network-scripts/ifcfg-enp0s3
echo GATEWAY=<ip of gateway> >> /etc/sysconfig/network-scripts/ifcfg-enp0s3
For example, to add a google DNS server the command would be:
echo DNS2=8.8.8.8 >> /etc/sysconfig/network-scripts/ifcfg-enp0s3
Now that you have installed WiKID, it's time to configure it. Start by running our script that configures or confirms your network settings and creates an SSL certificate for the WiKIDAdmin web UI.
wikidctl setup
Select that you want to change your network settings. We HIGHLY recommend you run through this and confirm your settings (unless the server is running on EC2 or a similar environment where the network is mapped externally). A self-signed SSL cert for the WiKIDAdmin will be generated. You can replace it later.
Select No for replication at this time.
The setup script will generate a dynamic password for the WiKID. Note this password! You can change it later under Configuration > Manage Administrators. If no dynamic password is created, use 2Factor.
NB: If you forget this password you can force change the WiKIDAdmin password by running:
/opt/WiKID/sbin/update_wikidadmin_passwd.sh -f
Once finished with the setup, start the server:
wikidctl start
The primary administration interface of the WiKID Strong Authentication Server is via the WiKIDAdmin web UI.
From a network-connected system, enter the URL address:
https://servername.domain.com/WiKIDAdmin/
Click through your browsers warnings about the self-signed certificate. The WiKIDAdmin portion of the URL is case-sensitive. You should see a screen similar to that shown in Figure 1.
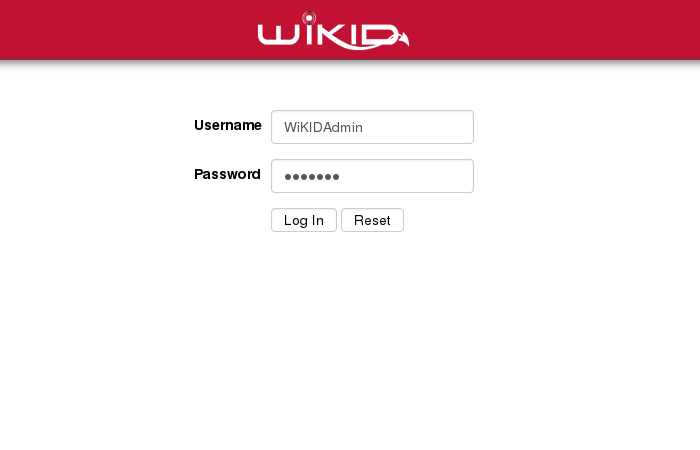
Figure 1 - Initial login screen
The default login credentials are:
Username: WiKIDAdmin (mixed-case) Password: 2Factor (mixed-case)
The main system status screen is shown upon successful login to the administration system as depicted in Figure 2. This screen provides summary information about the current status of the system and the services it provides.
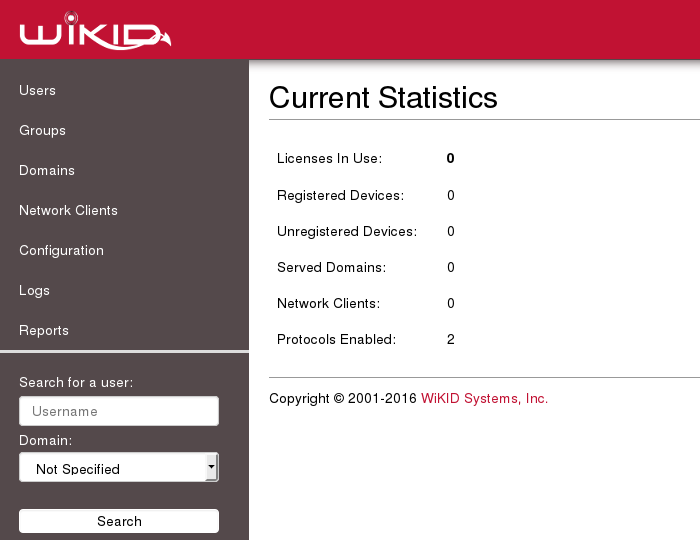
Figure 2 -Main Status Summary Screen
Each item is covered in greater detail later in this guide. In overview:
Registered Devices – This indicates the number of devices that are currently serviced by this server. These devices have completed the entire registration process and could successfully gain access to a secured resource.
Unregistered Devices – These devices have partially completed the setup process but have not completed the device to userid mapping. Unregistered devices are automatically purged from the system after 1 hour as specified in the RegCodeTTL paramater. This parameter can be changed in Configuration --> Set Parameters.
Served Domains – The number of distinct domains (server codes) configured for this server.
Network Clients – The number of systems that use this server for authentication. This includes both RADIUS systems and other protocols, such as wAuth. These are your VPNs, RADIUS servers, etc.
Protocols Enabled – The number of protocol modules installed and activated on the server. RADIUS is on by default and wAuth must always be enabled.
As we progress through this guide, we will periodically return to this status summary to note the changes in the values. This should provide a well founded understanding of the basic terms and concepts of the WiKID Authentication System. If you need additional background, please review the architecture of the WiKID's two-factor system.
IMPORTANT: Before moving on, please go to Configuration > Manage Administrators and change the Administrator password. You can also add more users.
Page Two: Create Certs.
