Setting Up the Certificate Chain
The WiKID system uses certificate authentication internally in several important ways:
- Each authentication server is also an intermediate certificate authority.
- Each authentication server uses certificate authentication to identify and authorize network clients.
- We use certificate extensions to manage user licensing and subscription terms.
NB: Once you get a cert, even an eval cert, it will be good for a long time. We add extensions to your cert on the CA site for licensing purposes. You add these extensions and then paste the updated cert into your server. You should not need to create a new signing request. If you need to replace a server, create a new signing request with a slightly different FQDN (it does not need to match the server name) and choose Replace the Server on the CA.
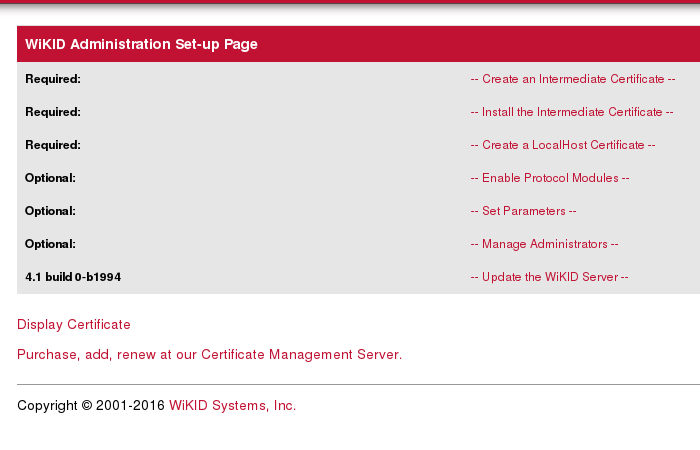
These functions require that a certificate be generated before the server is fully functional. This process is accomplished via the server’s administration interface. Select the – Creating an Intermediate CA - tab to access the certificate functions.
Step 1: Generate the Intermediate CA
The first step in the process is to generate the Public/Private keys that will be used to identify this server and to asymmetrically encrypt data via SSL. The server ships with a copy of the WiKID corporate CA certificate. This process will generate your keys and produce a certificate signing request or CSR. Select Generate and complete the form as described below.
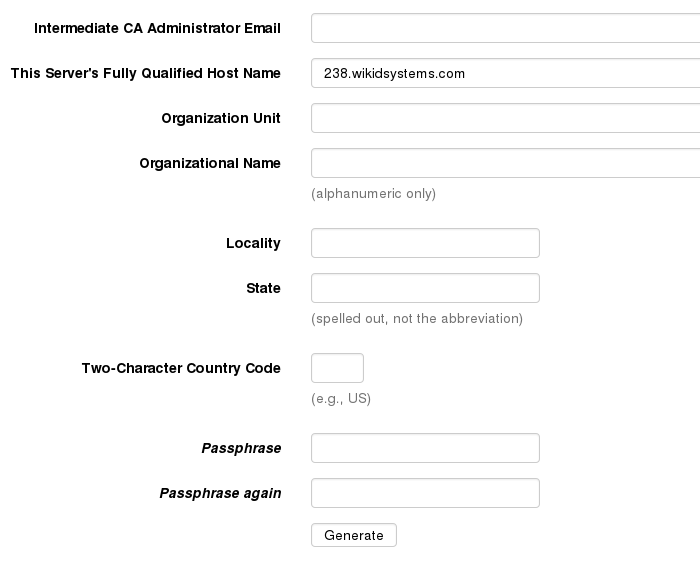
This form collects the information needed to generate a Certificate Signing Request (CSR) for this server. NOTE: All fields are required and the request must be unique (minor changes will create a unique request).
This should be the only time you use this form! You do not need to create a new CSR when renewing!
Field definitions:
Intermediate CA Administrator Email: This value provides a contact for delivery of the signed certificate. Please ensure this is a valid working email address.
Servers Fully Qualified Domain Name: This should be the server’s official registered name in DNS. SSL clients will expect the name given here to match the hostname that they use to connect to this server.
Organization Unit: Usually the department or division name. Used for identification only.
Organization Name: The name of the company operating this server. This should match the sales or evaluation unit records at WiKID to speed processing of the certificate issuance.
Locality: Generally the city name.
State: The state or province name. By convention this is not abbreviated.
Country Code: The official two-character code for the country. For the United States, this code is US.
Passphrase: This passphrase will be used to secure the private key in a PKCS12 armored file. It will be needed each time you start the server (it replaces ‘passphrase’ as the default passphrase to start the WiKID Server) to ensure the security and integrity of the server credentials. This value is never stored anywhere and cannot be recovered if lost. Select a strong and memorable passphrase and do not lose it.
Select generate to create the keys and the CSR. You should be presented with a screen similar to Figure 5.
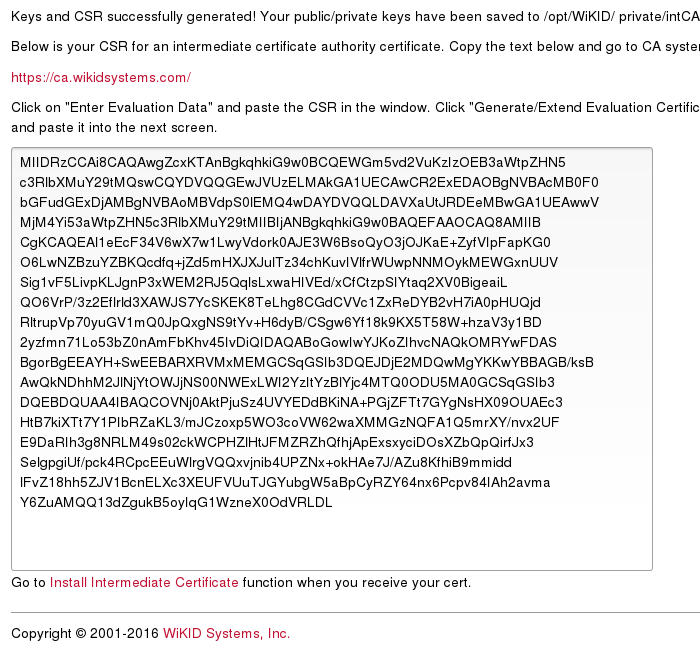
The Certificate Signing Request will be provided in base64 DER encoding. Select all of the text in the textbox and copy it to the clipboard.
Step 2: Submit the CSR for Signing
Click on the link to the Cert Management Server immediately above the text box (This URL may have changed). This will open the Certificate Signing Request submission page for the WiKID Systems Certificate Management Server. We'll be getting a 30-day Evaluation Certificate.
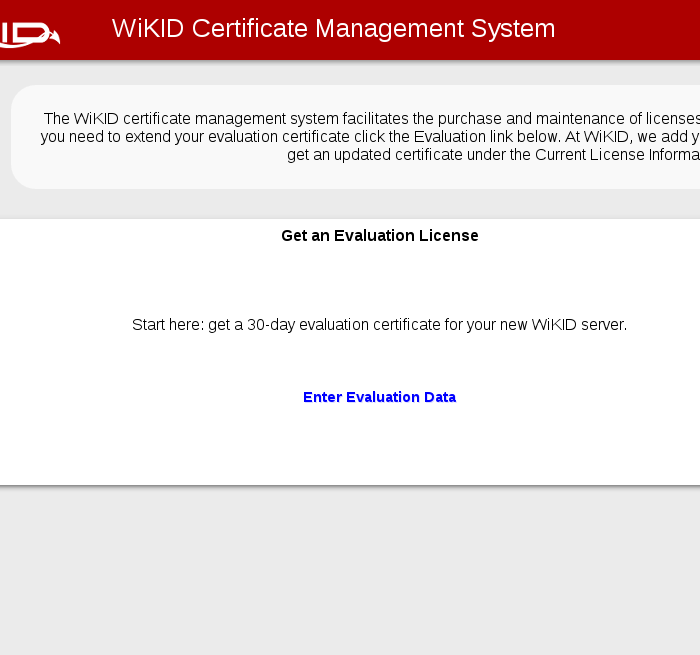
Click on the Enter Evaluation Data link. A box will appear. Paste your CSR into it.
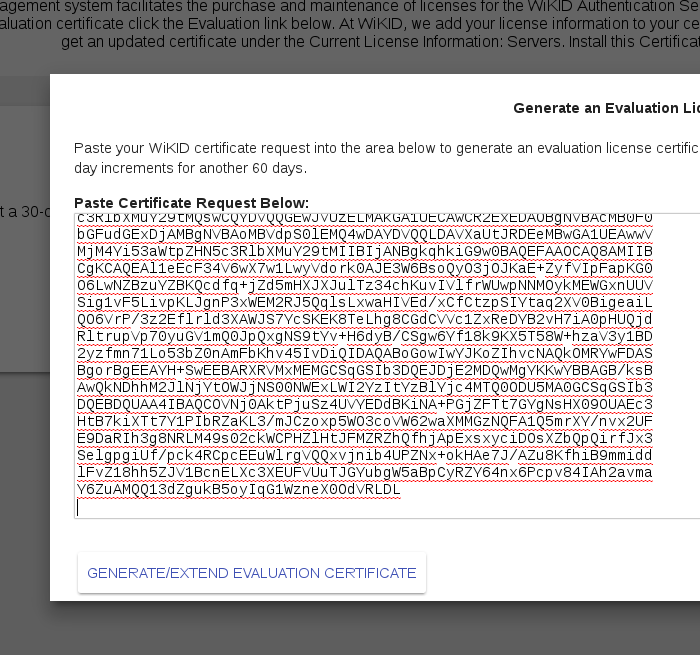
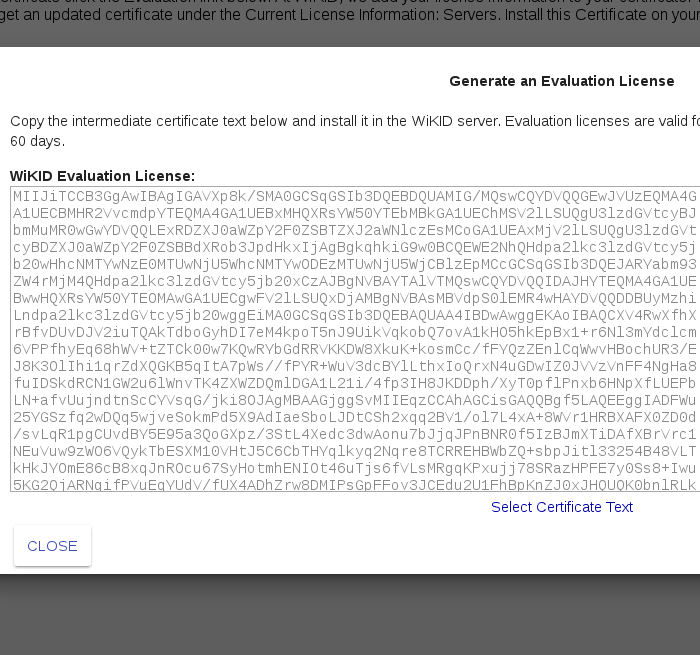
Click Generate/Extend Certificate. You will get back the Evaluation license. Click Select Certificate Text and right click/copy the cert.
Step 3: Install the Certificate
Back on the WiKID server, click on the link to Install the Intermediate Certificate. Paste the cert into the box and enter the passphrase.
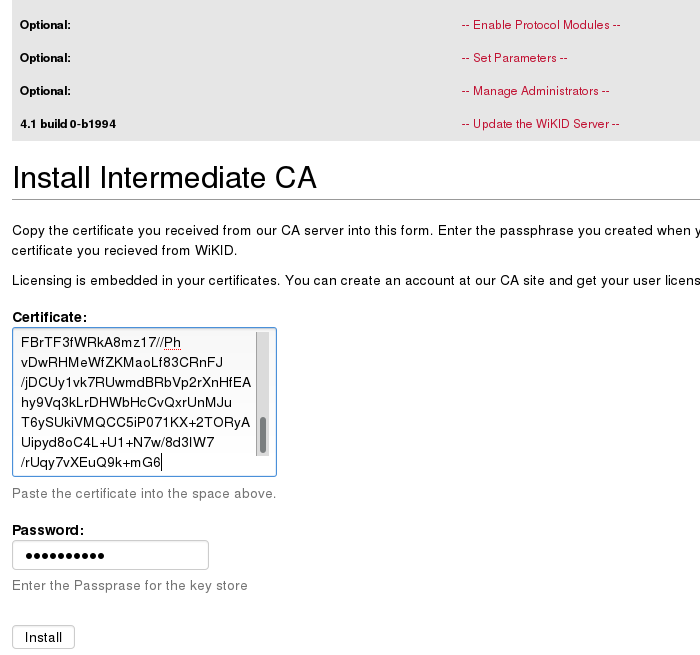
Click Install.
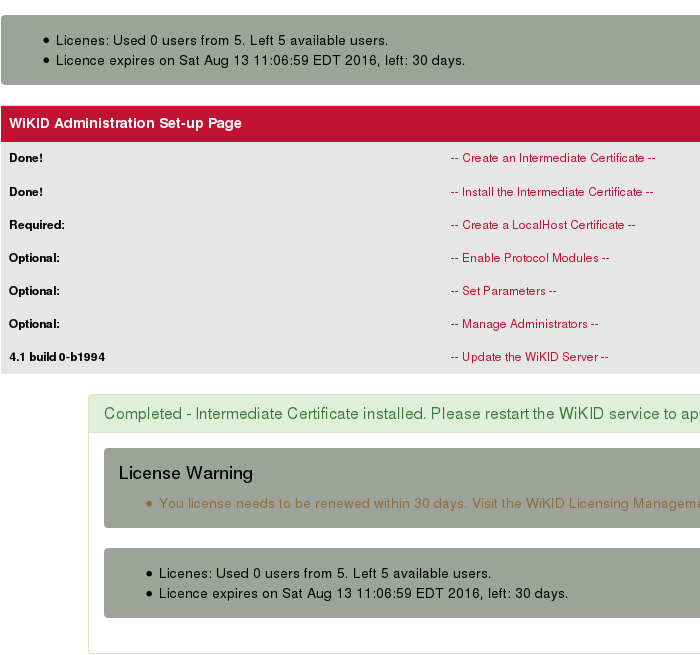
While it says to restart, we're going to do a bit more configuration and then restart.
Step 4: Generate a Localhost Certificate
All systems that communicate directly with the authentication server require a valid certificate issued by that server. Before these clients can access the server you must create a certificate signed by this intermediate CA. This prevents any unauthorized systems from communicating with the authentication server.
It is important to understand that some protocols such as RADIUS (for the Enterprise version), LDAP, wAuth, etc. do not provide facilities for certificate authentication or transport encryption. The WiKID Strong Authentication Server provides protocol modules that transparently convert these protocols into the secure communications required. This in turn means that the LDAP interface on the WiKID Strong Authentication serve requires a certificate to validate credentials even though RADIUS has no concept of certificates.
The protocol modules that run locally on the WiKID Strong Authentication Server itself may share a single certificate for localhost. You can create this certificate by specifying “localhost” as the fully qualified domain name at the generate certificate screen. It must be called “localhost”. This is illustrated below.
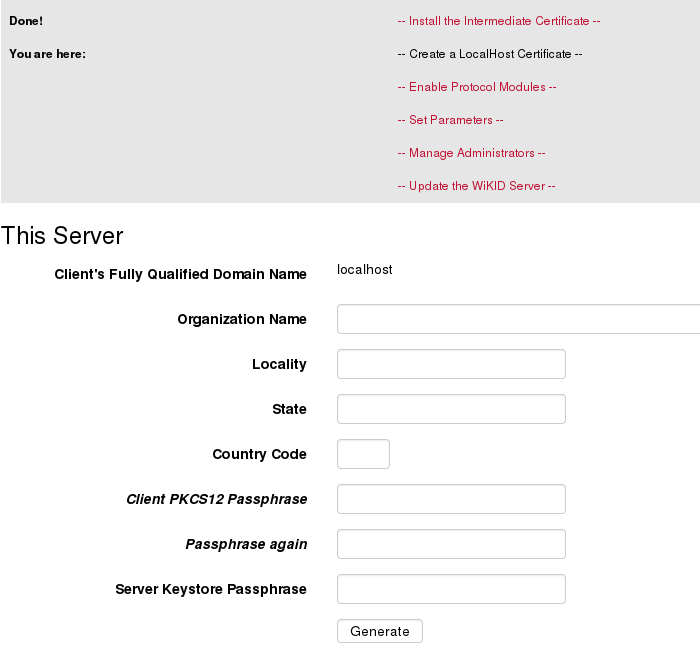
The values in this form signify the following:
Client’s Fully Qualified Domain Name: This is the name that the server will resolve when a client connection is made using this certificate. For local services it must be “localhost”.
Organization Name: The name of the company operating this client.
Locality: Generally the city name.
State: The state or province name. By convention this is not abbreviated.
Country Code: The official two character code for the country.
Client PKCS12 Passphrase: This is the passphrase that will armor the generated certificate.
Passphrase again: Repeat the Client PKCS12 Passphrase for verification.
Server Keystore Passphrase: This is the passphrase for the intermediate certificate authority that was created in Step 1.
Select Generate and you should be presented with a screen similar to this:
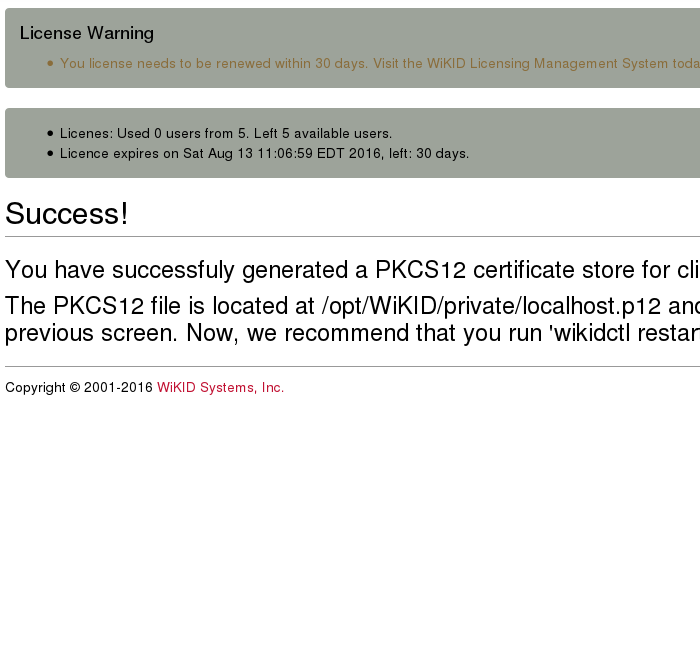
This message provides the location of the generated certificate.
NEW: note that since 99% of our deployments use only Radius, we have enabled it by default. We recommend against enabling LDAP or any unused protocol.
Page Three: Setup domains and network clients.
