Posted by:
root
8 years ago
The Verizon DBIR 2016 is out today and this is our obiligatory blog post. The usual caveats apply: it's a small (but growing) data set, there are reporting biases, etc, etc.
First, there's no better endorsement for two-factor authentication than the DBIR. 63% of all attacks used weak, default or stolen credentials. It is unclear what percentage of these credentials were for administrators, but the attack maps make it clear that the most common path is phishing > malware > stolen credntials > more bad stuff, so it seems safe to assume a good percentage are admin creds. Additionally, looking at the stolen credentials are used for exporting data and setting up command and control malware which indicates a high level of privilege.
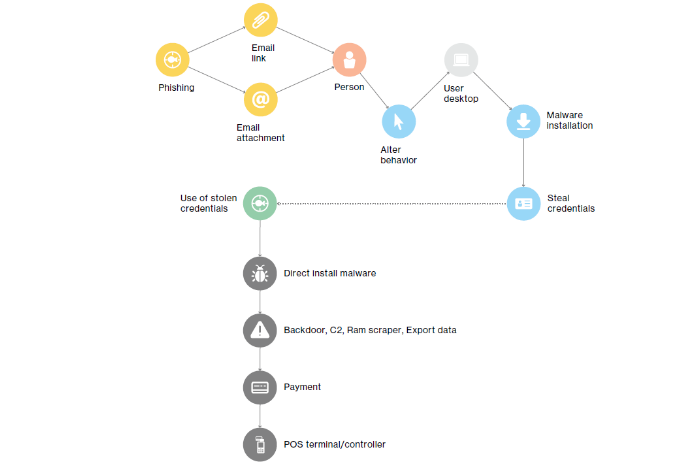
Source: Verizon DBIR 2016
It will be interesting to see what if any impact PCI-DSS 3.2 will have on this pattern. The DBIR notes that 27% of all incidents involve Payment Card Information. Will the new PCI requirement for 2FA for admins in the cardholder environment have an impact?
Share on Twitter Share on FacebookRecent Posts
- The latest WiKID version includes an SBOM
- WiKID 6 is released!
- Log4j CVE-2021-44228
- Questions about 2FA for AD admins
- WiKID Android tokens had their data deleted over the weekend by Google Chrome bug
Archive
2024
- January (1)
2022
- December (1)
2021
2019
2018
2017
2016
2015
2014
- December (2)
- November (3)
- October (3)
- September (5)
- August (4)
- July (5)
- June (5)
- May (2)
- April (2)
- March (2)
- February (3)
- January (1)
2013
2012
- December (1)
- November (1)
- October (5)
- September (1)
- August (1)
- June (2)
- May (2)
- April (1)
- March (2)
- February (3)
- January (1)
2011
2010
- December (2)
- November (3)
- October (3)
- September (4)
- August (1)
- July (1)
- June (3)
- May (3)
- April (1)
- March (1)
- February (6)
- January (3)
2009
- December (4)
- November (1)
- October (3)
- September (3)
- August (2)
- July (5)
- June (6)
- May (8)
- April (7)
- March (6)
- February (4)
- January (427)
2008
- December (1)
Categories
- PCI-DSS (2)
- Two-factor authentication (3)
Tags
- wireless-cellular-mobile-devices (7)
- Two-factor authentication (10)
- Wireless, cellular, mobile devices (6)
- NPS (1)
- Phishing and Fraud (111)
- Active Directory (1)
- pam-radius (3)
- privileged access (2)
- Cloud Security (10)
- Mutual Authentication (60)
- Web Application Authentication (1)
- Authentication Attacks (99)
- pci (50)
- Security and Economics (97)
- WiKID (133)
- pam (2)
- VPN (1)
- Installation (2)
- RADIUS Server (1)
- Open Source (64)
- Tutorial (2)
- Strong Authentication (35)
- Information Security (137)
- Transaction Authentication (13)
- Miscellaneous (100)
- Linux (2)
- transaction-authentication (6)
- Two Factor Authentication (254)
